Use MFA, Dammit!
I could say, "That's it. That's the post."
What are we talking about?
But I won't leave it at that. I will elaborate, because I feel I owe everyone a logical explanation of what MFA is, why it's so important, and how to do it right.
MFA stands for Multi-Factor Authentication. Authentication being the process of identifying yourself to the IT resource (device, program, or service) and establishing that you're the valid user of that resource. Broadly, there are three ways to authenticate yourself:
- Something you know (example: a password that matches to a user ID)
- Something you have (examples: a card with RFID, a magnetic stripe, or a chip)
- Something about you, physically (examples: a fingerprint or your face)
The guiding principle of MFA is, don't rely on just one. Usually two are enough, and so you may often see MFA referred to as 2FA.
Passwords
The first type, something you know, is the traditional way we have all become used to doing authentication. There are reams of advice out there about choosing good strong passwords. About using different passwords for each site. About giving over all your passwords to a password manager. And on and on it goes.
Maybe you're encountered password advice... or requirements... that's something like this:
- At least 8 characters
- At least three of:
- uppercase characters
- lowercase characters
- numeric characters
- Disney characters
- character flaws
- special characters (!@#$%^&*)
It's enough to drive you nuts. And the problem with this is, it actually pushes people in the direction of making worse passwords than they otherwise might. I knew a fellow on a job I worked at long ago whose password was the the name of his dog, plus a two digit number. Hey, it satisfied the requirements! We were required to change our passwords there every 90 days. (NOTE: This is another horrible practice, because it worsens the passwords people tend to make, even more than the composition requirements do.) Sure enough, each time he changed that dog-based password, he would just increment the number. So Keegan71 became Keegan72. The requirements were satisfied, and the security level was... Dopey.
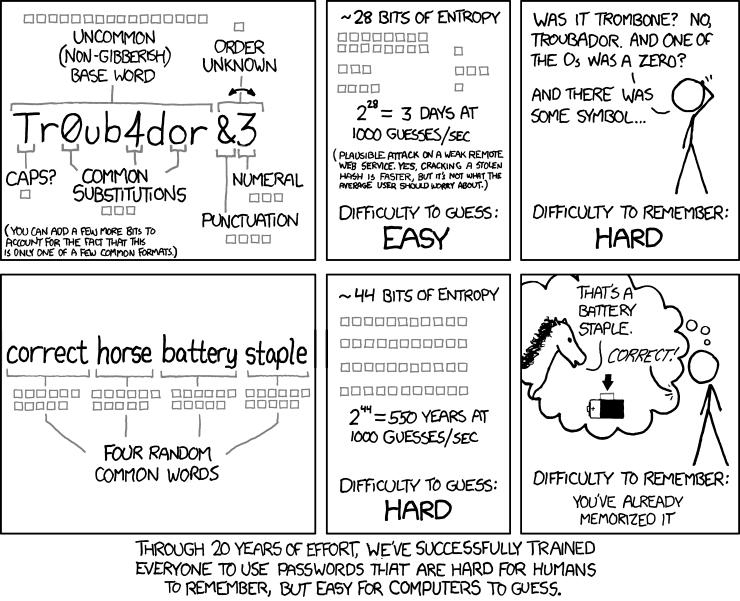
In 2017, Bill Burr, the NIST analyst who originally wrote those old rules we suffered under, apologized to all of us (paywalled WSJ piece: free-to-read summary here). If you still labor under these Goofy rules, show them this blog and tell them, "CISO-In-A-Box said, 'Let my people go!'"
I have been heartened in recent years to see better practices taking hold. A much better practice is: encourage people to make good pass phrases (30 characters long and more, but much easier to remember), and then only require changing them if there's reason to believe they have been compromised.
Because, oh yes, a password can get compromised no matter how strong it is. Perhaps the way it was stored was flawed. Perhaps the web page it was used on was vulnerable and gave it up. Or maybe the owner of that robust password got themselves beautifully phished. Doesn't matter... poof! Password in the hands of the bad guys, and trust me, they know what to do with it. The point is, none of these hazards is reduced in the slightest by how good the password itself is. Was. We want another line of defense. Enter, the second factor.
Second Factor to the Rescue
The second factor is one of the other items on the list above - either "Something you have" or "Something you are, physically". The beauty of these is they are what we call "out of band" - they are not in the same line of communication as the possibly-compromised password. Your face or your fingerprint, these are not with the attacker in another country who got your password by some nefarious means. They are right there with you. Likewise, your smart-card, or Yubikey are also there in your possession. When the attacker enters your ID and password, and then gets asked for the Yubikey, or the time-sensitive one-time pass-code from the app on your phone, well, they haven't got it. That'll slow them down, at the very least. Slowing them down is really the name of the game.
Quick side note: there are a LOT of ways that 2FA is being done nowadays. You might say, it's having a moment. But (surprise!) I have some opinions about a number of things I am seeing.
- Text Messages (SMS): You may have noticed, when calling the customer "service" team at your cell carrier, that you don't end up discussing your issue with the brightest bulbs on the tree. The bad guys have also noticed this. They can easily hoodwink those nice people into sending them a SIM that mimics yours, and then they get your text messages, too. Your safety factor from getting a text with a six-digit code to enter when you log in is now a complete zero to them.
- "Push" notifications: These are subject to being compromised when the clever criminal with an ill-gotten copy of someone's password starts generating lots of prompts, at a high rate. The poor schnook's phone is blowing up. Bleep! Bleep! Bleep! Sooner or later, out of exasperation, exhaustion, or just pure fat-fingering, the owner of the password clicks "Yes." Once. The phone goes quiet. This sounds good but... it is very, very bad. For reference, this is precisely how LastPass got breached, last summer.
- Email: Ugh. This is so 1990. Can it please stop now? The way I see this: if the bad guy has your application password, he PROBABLY also has your email password. There's no way a code sent via email is protecting anything, any longer.
On the other hand, if the app on your phone is producing a timed set of six new random digits every X seconds, there's a beautiful simplicity at work here: No data is flowing to make that happen. The phone and the web application exchanged a secret weeks or months ago when you set it up. That started a long sequence of timed changes which your phone and the web app are reproducing in parallel, but independently. Having the clone of your SIM does not help the attacker with this. Attacker would have to go back in time and somehow spy on that one-time secret exchange. It's not feasible.
No system is perfect. If you notice the name of the blog where you are reading this is "Safer Computing." Not "Safe Computing." But getting away from single-factor will greatly improve your odds in this ever-escalating arms race. And that, to me, is a win.