Hacker ≠ Criminal!
Whenever a news story breaks about information security (usually a radically bad FAILURE thereof) then "security researchers" or "consultants" get trotted out by the media to give expert soundbites. David Kennedy was a keynote speaker at the recently-concluded Rochester Security Summit, so he'll do for my example:
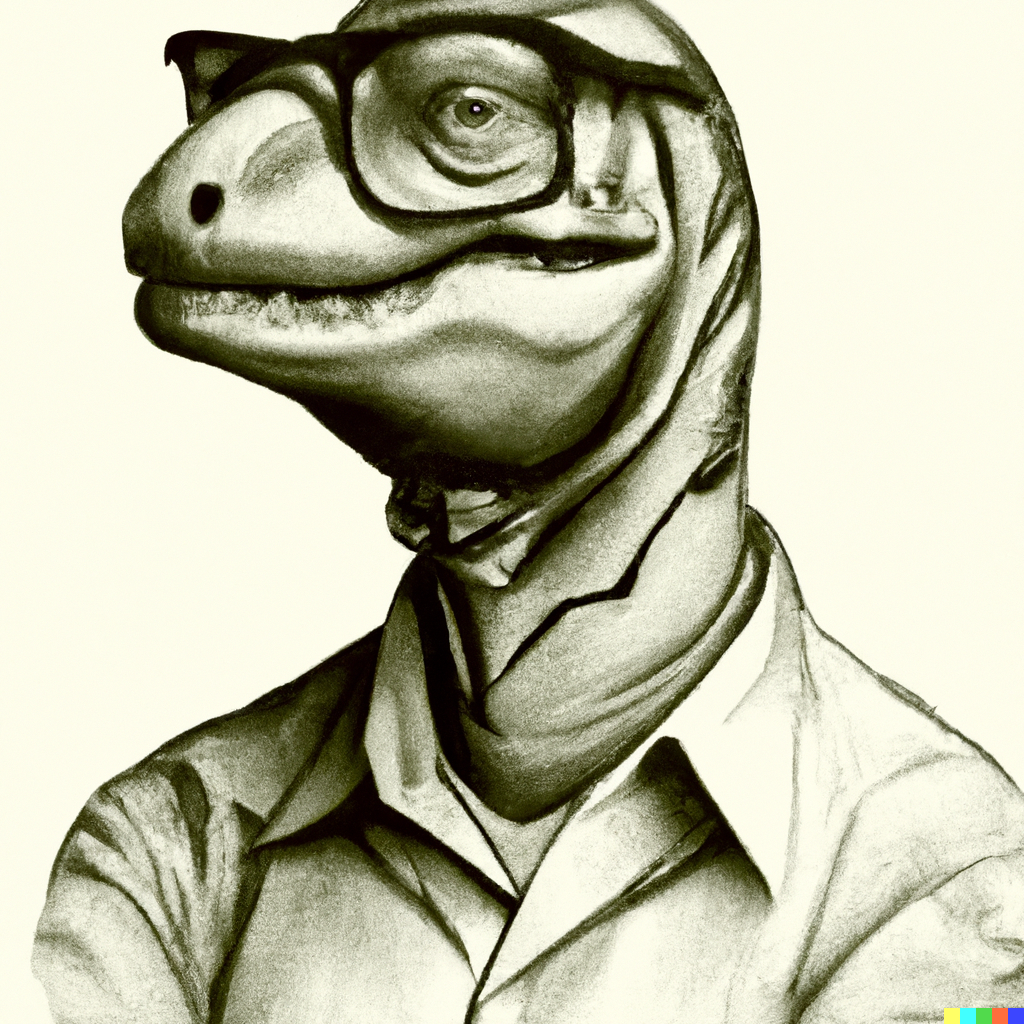
TrustedSec's David Kennedy on CNN from David Kennedy on Vimeo. David is a security researcher - which means he's a hacker. No, I did not just accuse him of a crime. He's a wonderful guy and I would totally invite him to dinner.The media have abused the the term "hacker" for years now. The original meaning of the word was simply, "One who is expert at programming and solving problems with a computer." That expertise, together with an insatiable curiosity driving one to exercise it, is what genuinely makes a hacker.
Cyber-criminals may or may not be hackers. For example, if they wish to crack their way into some company in order to plunder its money or sensitive info, they might exercise their own high levels of technical skill. But they might hire technical capability, and not exercise it themselves. Or they might be what we call script-kiddies, people who find easy step-by-step recipes for creating digital mayhem, and use them to good effect against poorly secured targets. They might not even be criminals: they might be state-sponsored, and thus their actions are legal. At least under their nation’s laws.
Hacking is a set of problem-solving approaches, and a toolbox of techniques. It's a way to accomplish a goal, and the goal's goodness or badness is not relevant. Hacking is morally neutral. If, and only if, the goal of the hacking is a crime, then a hacker also happens to be a criminal. Security researchers (like David) are employed to find ways that our information systems can be exploited. They might do malware reverse-engineering, or vulnerability discovery and analysis, or refining social engineering techniques. Most of our companies don’t employ them: it’s too specialized. Large providers and specialty firms (Verizon, FireEye) provide researcher talent, and we consume the output in the form of reports and alerts. Independent researchers also work as consultants. They may help companies figure out what happened after an attack, or they may routinely provide bug reports to manufacturers. They may work on Red/Blue team exercises, where attacks are simulated and defenses are tested.
Without question, Security Researchers are hackers. If they aren't, they cannot function in that job.